The operational tempo of the enterprise in cyberspace demands engagement of protections in cyber-relevant time. No longer can enterprises depend on human-driven processes to address the ever-increasing number of cyber events across the exponential number of devices that must be managed. Innovations in cyber threat intelligence; predictive analytics; situational awareness through artificial intelligence / machine learning (AI/ML); automated event response orchestration; zero-trust networks; and, trusted data sources are the new capabilities that must be leveraged to meet these increasing demands in cyberspace. Learn a new concept of operations called active cyber defense that defines how cyber security for the next generation enterprise must operate.
iDefense – the next generation Active Cyber Defense
Today’s human-driven cyber response processes are hampered by several problems:
- The need for continual analysis of large amounts of dynamic data to develop actionable cyber intelligence
- Insufficient pattern recognition and behavioral analysis across different data streams from many channels and across different management silos
- Lack of visibility of the complete conditions of the IT / network environment
- Lack of insights into possible threats and ability to recognize systems compromise in cyber relevant time
- Insufficient ability to manage resiliency of systems to attacks
- Difficult and time-consuming efforts in dealing with operational complexity and impact analysis – Will updating a host-based security policy cause an outage?
The problems of finding, confronting and defeating a cyber adversary are generally difficult enough for today’s traditional IT systems. However the problems are even worse for industrial control systems (ICS), Internet-connected consumer devices, medical devices, and other embedded systems being deployed as part of the Internet of Things (IoT). Many of these systems are unmanaged and unmanageable; however, they are vulnerable to cyber-attack, as evidenced by the recent Mirai botnet DDOS attack. Vendors of these IoT/ICS systems claim lack of financial or regulatory incentives to secure them, while, at the same time, system operators choose to connect these systems to the Internet for convenience and business reasons. The result is wide open critical infrastructure systems ripe for cyber-attack.
Basically, the cyber security challenges facing enterprises are divided into five buckets:
-
- Resources
A talent gap of highly skilled cyber analysts and engineers is repeatedly cited as a major issue for organizations combatting cyber threats. This talent gap is exacerbated by the increasing volume of cyber events that must be triaged, investigated and resolved. Adding new sensors and threat information sources is difficult when the existing staff of analysts is already over-burdened by the existing workload.
-
- Products
Security defense strategies are complicated by the myriad of tools offered by vendors and implemented by users. Tools identify assets, scan for vulnerabilities, patch, remediate, protect the network, manage access control, encrypt data, log events, and much more. As noted by Dr. Gene Spafford, the founder and executive director of Purdue University’s Center for Education and Research in Information Assurance and Security (CERIAS), “… poorly coded software combined with growing network complexity has increased the attack surface at many organizations. This has resulted in using all these [security] tools on a regular basis because the underlying software isn’t trustworthy.” All too often security tools do not integrate well with each other and only cover a subset of the assets that need to be protected. These coverage gaps result in loss of situational awareness, difficulties in defending against attacks, and slow response processes.
-
- Timeliness
Generally, playbooks for incident response are exercised manually with workflow triggered and maintained by a ticketing system. Mitigations are delayed as tickets get escalated and lost amid confusing hand-offs between functional silos. Often, change management boards must be consulted prior to manual modifications to systems. This manually-intensive workflow system creates significant latency in incident responses, potentially allowing cyber adversaries time to pivot and to burrow into the network.
-
- Technology churn
Cloud computing and mobile computing are two trends that are at the forefront of technology churn. These trends change the security paradigm, creating a perimeter-less environment as content and applications move outside of the traditional enterprise boundaries. These changes ripple throughout the entire enterprise, creating significant changes to other impacted systems as well as to traditional risk assessment and mitigation models. Technology churn is an important issue affecting the security operations centers’ ability to turn the corner on the cyber security problem.
-
- Costs
Each of the buckets listed above lead to ever-growing costs for cyber protection without generating any clear-cut gains for defending the network and assets from threats.
In the end, many enterprises are still mired in a static/reactive protection model whose main focus is on prevention of attacks. As current evidence suggests, a prevention strategy eventually fails. A new “proactive” strategy is needed to detect and contain threats before they can seriously impact enterprise operations. The strategy must enable early disruption of the “kill chain” and provide prioritized and automated responses to critical threats to gain positive control over attack consequences. Enterprises need to better predict attacks by using analytics (to provide early and accurate recognition of anomalous and malicious behaviors). Enterprises need to align defenses to these predicted attack vectors, and remove the cloak of stealth that attackers currently enjoy. The way ahead requires better cognitive systems for threat recognition and attribution, smart systems-of-systems interactions, and autonomous security capabilities. The future of cybersecurity is Active Cyber Defense (ACD).
ACD Enables Defensive Responses in Cyber-Relevant Time
The U.S. Department of Defense (DoD) strategy for operating in cyberspace expresses the need for Active Cyber Defense (ACD), and defines ACD as: “DoD’s synchronized, real-time capability to discover, detect, analyze and mitigate threats and vulnerabilities.” The key tenet of ACD is responding to cyber events in cyber-relevant time. Cyber-relevant time is a term that encompasses a range from milliseconds to minutes depending on where the cyber event is handled. If the event occurs within a computer’s central processing unit (CPU), we’re talking microseconds. If the event involves an attack between two computers separated by a satellite we’re talking milliseconds to seconds; add live operators and we’re talking seconds to minutes. The point of ACD is to execute a defensive course of action before an adversary can bring about their desired result. This requires a semi-autonomous system that augments the ability of defenders to detect and stop attacks while minimizing manual intervention in the process. Human cognition of cyber events must be facilitated through visual interactive analytics and artificial intelligence / machine learning in the decision-making process. ACD also pushes the decision-making out to the endpoint when that makes sense and when intelligent agents on the endpoint can effect an appropriate response.
ACD is enabled by seven innovative technology advancements:
|
# |
Innovation |
Description |
ACD Differentiator |
|
1 |
Analytics | On-premise or cloud-based correlation of cyber events to detect anomalous behavior and evaluate risk | Risk-based analytics enable better decision-making for responding to cyber events |
|
2 |
Machine Learning / Artificial Intelligence | Applications of ML/AI that augment human-based situational awareness and the selection of cyber COAs based on mission risk parameters | Quality of Cyber COAs improve through application of ML/AI within a risk-managed situational awareness framework |
|
3 |
Automated Orchestration | Cyber Courses of Action (COAs) are automated and shared; with human-in-loop when needed | Speed of response and quality of COAs improve through automation and sharing of COAs |
|
4 |
Threat-Informed Defenses | Threat indicators are used to inform selection of COAs and are shared within a trust community | Cyber hunt capabilities are enhanced through threat indicators and related analytics |
|
5 |
Real-time Risk Management | Security posture and security configurations are automatically updated when COAs are implemented | Security configuration compliance is maintained in a dynamic environment |
|
6 |
Zero Trust Networks / Identity-Based Networking | Networks are cloaked and segmented; all traffic is inspected and controlled on a fine-tuned basis | Mission assurance and resiliency are enhanced in contested cyber environments |
|
7 |
Distributed Security Manager / Block Chain Technology | Distributed security manager provides trusted Cyber C2, trusted data sources, trusted file sharing and intrusion tolerance for distributed operations | Mission assurance and resiliency are delivered to distributed operations (IoT/mobile/ICS) |
ACD Framework
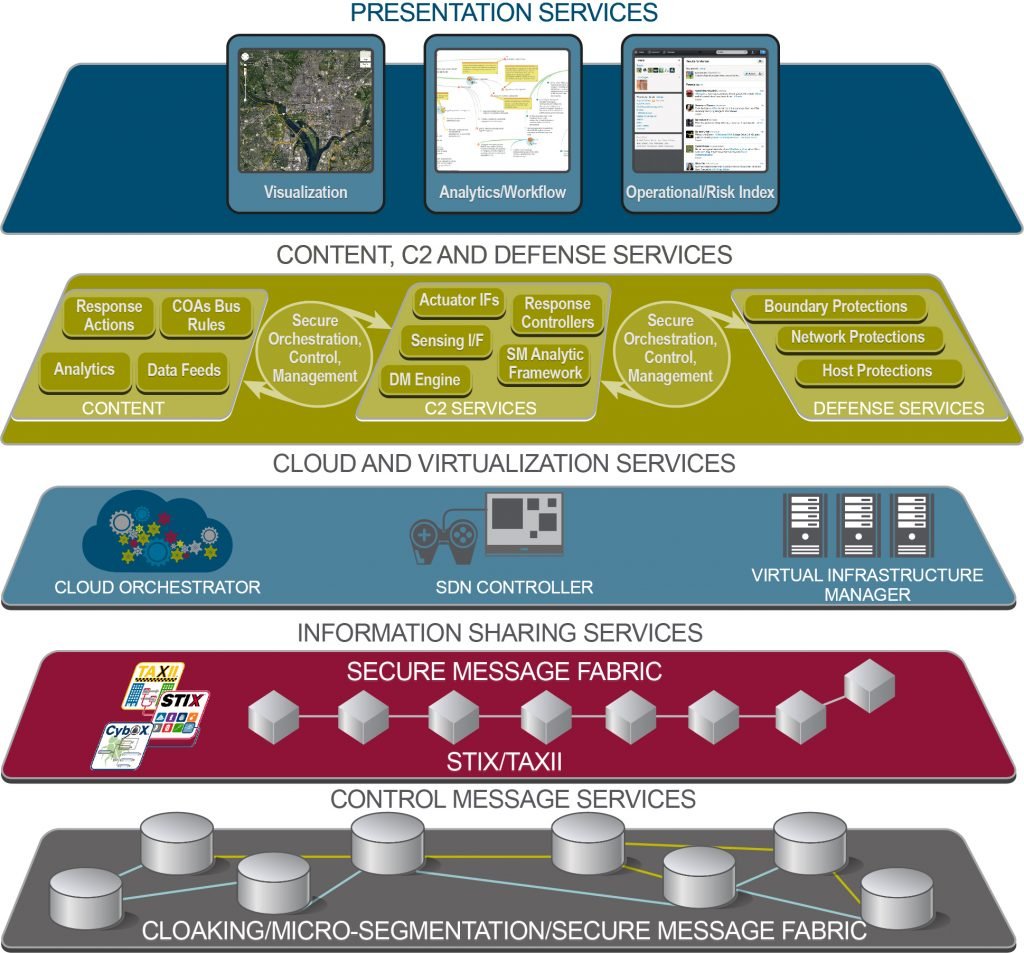
The figure below is an example of an ACD framework. It is based on efforts underway by NSA and includes major contributions from researchers at the Johns Hopkins University Applied Physics Laboratory (APL), DoD, DHS, and industry vendors. The framework also reflects collaborative work products by the OpenC2 Working Group which is developing a standard COA command language syntax and semantics. The figure below extends the NSA ACD Framework to include Cloud and Virtualization Services along with specific capabilities for assuring C2 messaging and sharing. A summary description of each of the major elements of the extended ACD framework is provided below.
The upper layer of the framework consists of Presentation Services. This layer includes risk/operational dashboards, models and simulation tools, and workflow systems that provide the visualization and situational awareness to track and manage cyber events and incident response status. Two of the key visualizations at this layer are the risk index (RI) and operational performance index (OPI). These indices are like thermostat dials where the current temperature is recorded and you can set the threshold for heat. For the risk index, a measure of the selected organizational mission’s risk posture is listed and you can set your appetite for risk based on the circumstances around your mission, such as Infocon levels. The OPI reflects your overall infrastructure readiness to support the enterprise mission.
The next layer of the framework contains ACD Content, Command and Control (C2) Services, and Defense Services for sensing and responding to cyber events, as depicted in the following figure. 
ACD Content includes data feeds such as vulnerability information, indicators of compromise or attack, and assets’ configuration state from network and host-based sensors. These data feeds are rapidly and continuously ingested into repositories and classified for review.
ACD C2 Services include:
- A sense-making analytic framework that adds context around cyber event data.
The sense-making framework integrates different tools and repositories of data, such as security information and event management (SIEM) tools, log aggregation tools, and user entity behavior analysis (UEBA) tools and applies real-time diagnostics to add context to cyber events. The heart of its diagnostics capability is a mission monitor tool that maps events to a mission-task-asset graph to understand the impact of a cyber event. Its output is an appraisal of risk at any point in time and an assessment of the enterprise’s ability to execute its mission.
- A decision-making engine that takes in actionable intelligence output by the sense-making engine and applies artificial intelligence guided by business/risk management rules to assemble appropriate COA(s) for execution.
The decision-making system uses pre-formulated response actions to create courses of action (COAs), or playbooks, that are designed to quickly mitigate incidents, stop attacks, patch vulnerabilities, or contain damage while meeting mission assurance goals. COAs are published to response controllers using a standard command and control (C2) language. The decision-making engine includes a machine learning component to augment human cognition for selection of the appropriate COA and to improve decision-making over time
- Response controllers to orchestrate the execution of COAs for specific Defense Services components.
Response controllers choreograph an intelligent network of security capabilities to respond to security events using the COAs provided by the decision-making command element. Actuators conduct “cyber maneuvers” to reduce the attack surface and respond to attacks by executing COAs. The loop is closed by the sensing mechanisms which monitor failure or success of directed actions.
- Interfaces for actuators and sensors.
Open APIs and connectors are needed to translate cyber C2 commands/data feeds and connect the “sense-making” and “decision-making” portions of the ACD capabilities with the “sensing” and “acting” capabilities.
Defense Services consist of the host, network, and boundary protection capabilities that sense events; or, are actuated to mitigate a threat or remediate vulnerability condition. Defense Services are orchestrated by direction of the respective response controller(s).
The middle layer of the ACD framework is Cloud and Virtualization Services. Cloud and Virtualization Services consist of three managers: the Service Orchestrator, the SDN Controller, and the Virtual Infrastructure Manager. The ACD Response Controllers interact with the Service Orchestrator to direct security-related actions that operate at this layer. The SDN controller also works with the Service Orchestrator to create logical networks linked to virtual workloads managed by the Virtual Infrastructure Manager. Security services are virtualized and attached to workload virtual machines (VMs). As workload is moved to another host, these security services stay attached to the workload VM and move with it. As new VMs are added to a network, a security policy can be dynamically applied to the new VMs using the interoperation of the ACD response controller and the Service Orchestrator.
In SDN environments, the control plane understands the network schematic and is therefore able to configure the network in response to specified commands. The control plane creates an overlay — a temporary logical network put in place to address a demand, a situation, or a security response — without having to touch the physical underlay. The control plane also choreographs the VNFs enabling them to be scaled up or down. This dynamic level of control allows an administrator to re-prioritize or even block specific types of packets with a very granular level of precision.
The capability of SDN to enable service chaining for dynamic network adaptation is a key enabler from an ACD perspective. Service chaining allows for fine-tuning of protection parameters based on specific virtual workloads and traffic flow patterns. Network operators can develop a behavior-based view of network activity, which facilitates learning and anticipating the “normal” traffic conditions for time-of-day network needs. Security policies can be fine-tuned to these normal behavior profiles and COAs can be developed to possible changes before they occur. Then, when anomalies, security events, or changes in resource utilization actually occur, the SDN controller can sense and analyze these changes and allocate dynamic countermeasures based on service chained security functions as directed by the ACD Response Controllers. If a failure or a compromise does occur, the network can deploy courses of action consisting of virtualized, service-chained network and security functions to quickly self-heal or contain the threat, determine the root cause, and implement mitigations.
The Information Sharing Services layer is a standards-based capability that facilitates sharing of cyber intelligence (attack or compromise indicator information) among a trust community using the STIX/TAXII standards. These standards are also being purposed to share anonymized COA information among community of trust members or within an enterprise (e.g., between different SOCs). For example, threat indicators or anonymized COAs may be shared among participating members of the Defense Industrial Base Network (DIBNet) which is a DoD community of trust.
Cyber intelligence is most useful if its accuracy and relevancy can be quickly ascertained and translated into action at network speeds. Therefore, it is critical that cyber intelligence gathering, sharing and distribution are accomplished seamlessly, and applied at machine speeds. STIX/TAXII are a family of standard specifications to automate the conversion of threat data into actionable intelligence. These standards and specifications include:
- STIX™ — an extensible markup language (XML) standard to automate the sharing of threat intelligence.
- TAXII™ — a set of technical specifications that enable organizations to exchange and securely transport cyber threat information represented as STIX.
- CAPEC™ — Common Attack Pattern Enumeration and Classification: a publicly available, community-developed list of common attack patterns along with a comprehensive schema and classification taxonomy.
- MAEC™ — Malware Attribute Enumeration and Characterization: a standardized language for encoding and communicating high-fidelity information about malware based upon attributes such as behaviors, artifacts, and attack patterns.
- CybOX™ — Cyber Observable eXpression: a standardized language for encoding and communicating information about cyber observables.
STIX, CAPEC, and MAEC each use CybOX to describe cyber observables. A cyber observable is a measurable event or stateful property in the cyber domain. Examples of measurable events include: a registry key is created, a file is deleted, or a hypertext transfer protocol (HTTP) GET [requests data from a specified resource] is received. Examples of stateful properties include: the value of a registry key, the MD5 hash of a file, the existence of a mutex. The CybOX schema is natively imported and used within STIX, CAPEC, and MAEC to characterize system and network events and behaviors observed within the operational cyber domain.
The Control Message Services layer is intended to decouple C2 Services from Defense Services to enable a more seamless plug and play capability. It is also intended to facilitate trusted and secure channels between the different services and layers of the ACD framework. For example, the Control Message Services will help enable secure machine-to-machine sharing of threat information between different enterprises in a community of trust.
There are three capabilities that comprise the Control Message Services:
- Zero-trust network using a diverse set of IBN infrastructure tools to enable cloaking and micro-segmentation of the network
- Basic Messaging Transport based on capabilities such as ActiveMQ, RabbitMQ, TLS, etc.
- Secure Message Fabric based on distributed ledger technology (Blockchain) and related consensus and messaging protocols.
Further descriptions of the zero-trust network infrastructure tools, and the Secure Message Fabric are provided below.
Zero-Trust Infrastructure
It is imperative that C2 Services are reliable and secure between the components of an ACD environment. For this reason, the ACD framework proposed by ActiveCyber incorporates three diverse zero-trust network infrastructure tools to only permit authenticated trusted network connections while cloaking and segmenting the network for added protection. These tools include Cryptonite NXT for Internet-facing domains; Tempered Networks’ Host Identity Protocol (HIP) appliances for internal domain segmentation; and BlackRidge Technologies’ Transport Access Control (TAC) to authenticate and cloak C2 communications within Cloud and Virtualization Services. Each of these technologies implements a form of Identity-Based Networking (IBN) where a user’s identity is somehow tied into the networking services that the user can receive.
Cryptonite NXT uses two technologies which work together to amplify boundary network defense:
- Moving Target Defense (MTD)
Rather than allowing a protected endpoint or a malicious device to see the real network, Cryptonite NXT transforms the endpoint’s view of the network into a dynamic, abstract structure, in effect making the once static network into a dynamic moving target. Normal legitimate traffic is unaffected by MTD. However, MTD severely restricts an attacker’s ability to collect actionable information about the network, or to masquerade as a legitimate endpoint. Thus, MTD substantially increases the attacker’s time, effort, and risk necessary to establish or maintain a presence in a network. The validity of any information garnered by an attacker is also restricted to a limited period of time, making it necessary for the attacker to repeatedly perform reconnaissance. Cryptonite NXT’s moving target defense performs cryptographic verification of all packets and authentication of the sender to allow authorized users in and to keep attackers out.
- Attack Surface Segmentation
MTD creates a mapping from the cloaked network to the real network, known only to Cryptonite NXT, to enable flow of traffic across the traditional network infrastructure. Attack Surface Segmentation creates a decision point regarding whether a packet should be permitted through that mapping. This decision minimizes exposure and contains attacks while allowing legitimate communications to take place. At a per-user and per-service level, Cryptonite NXT decides at line speed whether a given packet needs to be permitted through the network. Unless absolutely necessary, the packet is not delivered to the endpoint thereby preventing malicious packets from ever reaching a protected endpoint. As with MTD, this protection is always on at every endpoint.
Cryptonite NXT is agentless; nothing is installed on endpoints or servers. It supports all IP-enabled devices. It protects traditionally unprotected devices including printers and legacy devices.
Internal domain segmentation and cloaking services are provided using Tempered Networks’ HIPswitch, HIPapplications, and HIPclients. These technologies are based on the Host Identity Protocol (HIP) – an IETF standard – to create an Identity-Based Network (IBN). Using HIP, the IBN gives trusted cryptographic identities to machines and networks and enables management of communications between those identities in a highly dynamic and scalable way through a centrally controlled automated orchestration engine. The encrypted and trusted IBN fabric enables secure connectivity across physical, virtual, and cloud domains.
HIP introduces the concept of an identifier-locator split (separating the role of IP addresses as host identity and topological location in the Internet), where hosts are identified using strong cryptographic identities in the form of 2048-bit RSA public keys. The locator is an IPv4 or IPv6 address, but the identity is not tied to the identity of the host. Hosts can change their IP location, but retain their strong cryptographic identity. HIP remains compatible with IPv4 and IPv6 applications, utilizing a customized IPsec tunnel mode for confidentiality, authentication, and integrity of network applications.
Because cryptographic identities are used for trusted communications rather than spoofable IP addresses, it doesn’t matter what IP address was originally assigned to the device. HIP effectively decouples the transport layer from the network layer, and allows the upper layers of the stack to use a Host Identity (HI) in their socket APIs instead of an IP address. A new IP address is provided that follows the device around the world. This dynamic traffic management allows admins to move IP addresses of machines, or move the machines with their IP address, anywhere in the world, to any network, without making any routing changes or creating complexity.
By partitioning and isolating the network into trusted micro-segments, Tempered Networks completely cloaks vulnerable infrastructure from outside users, without the difficulty of having to individually update each connected device. Devices that are cloaked are undetectable from the underlying network. Tempered Networks’ HIPswitch™ security appliances (physical or virtual) are deployed in front of any IP-connected devices and systems to create private, encrypted overlay networks. Starting with zero trust, the solution allows users to whitelist devices for explicitly trusted and encrypted communications between HIPswitch appliances.
The ACD Framework secures C2 communications within Cloud and Virtualization Services using BlackRidge Technologies’ Transport Access Control (TAC). For example, TAC provides cloaking and authentication services between the ACD Orchestrator and the Virtualization Service Orchestrator or the SDN Controller. It also secures C2 communications between the SDN controller and respective Virtual Network Functions (VNFs).
TAC separates security policy from the network design by applying identity to authenticate network sessions before connections are established, allowing only identified and authorized traffic to proceed. It is based on RFC 4226 – HMAC One-Time Password (HOTP) algorithm. When a TCP/IP connection is initiated on the client, the TAC client intercepts the setup and takes an identity seed, hashes it to a 32 byte length, and inserts it into the first packet of the session (the first packet token replaces the random sequence number of the TCP connection setup). A server gateway will disregard (or based on policy, redirect) any packets until it receives the identity token. Once it receives the token, it validates the identity of the requester and then lets the traffic pass. The gateway acts in bridge mode.
TAC requires no modification to existing network applications or servers, and is compatible with existing security and authentication technologies, including IPsec and SSL/TLS VPNs, firewalls, IDS and IPS systems and routers. TAC adds zero overhead to network traffic and works with IPv4, IPv6 as well as a variety of network architectures including client/server, server/server, cloud, mesh, flat, and asymmetrically routed networks.
BlackRidge TAC can be deployed in 1G to 100G network configurations as virtual or physical gateways that provide high throughput with low latency compared with next generation firewall and malware inspection tools. TAC is scalable to support millions of identities while providing low, deterministic latency. The token cache is tolerant of packet loss and enables TAC deployments in low bandwidth and high packet loss environments as well.
TAC effectively cloaks the server from recon by attackers and stops cyber-attacks by blocking scanning and reconnaissance. It therefore effectively rids the traffic of noise making downstream Deep Packet Inspection capabilities more effective. It also helps mitigate Distributed Denial-of-Service (DDOS) attacks since no handshakes are created with untrusted users.
ACD C2 Services Must Move to the Mobile Edge
The nexgen enterprise will be increasingly mobile and the demand for bandwidth intensive mobile voice and data capabilities will continue to stress RF-based capabilities. Maintaining secure and available communications at the mobile edge will be tested as spectrum is squeezed. The IoT will also bring new challenges for seamless reconnect while mobile and the capacity of backhaul transport to scale for the management of IoT devices.
The mobile edge contains your mobile platforms and devices, your sensor grid, your IoT devices at your campus or scattered in the field / at sea. What to note is the dynamic operations that occur at the edge and where optimization of resources is essential – spectrum and SWAP ratios must be managed. This domain also requires elasticity for surges and distributed capabilities to handle responses to adversarial operations. These challenges can realistically only be met if C2 Services move closer to the edge.
The following chart highlights some possible approaches to enabling capacity and security at the mobile edge.

From a spectrum perspective, the use of femto-cells (smaller cells) to increase spectral reuse will lead to a 10x increase in the number of network devices. Optimization and management solutions that can target this increase should be handled by technologies such as analytics, SDN and NFV orchestration (NFVO). Additionally, since better wireless algorithms (e.g., MIMO and other signal processing) are required to increase spectral efficiency, 10x computational power increases are expected for future wireless standards. Here a cloudlet model through the employment of virtual radio access networks (vRAN) could provide the elasticity needed to handle the additional compute at the edge while also helping to address the SWAP issues and the need for agility to handle different wireless protocol stacks.
From a backhaul perspective, backhaul bits are expensive, and more value needs to be squeezed out of every backhaul bit. IP local breakout and Secure Message Fabric services at the wireless edge will allow superior quality of experience (QoE) and security for mobile enterprise users. The following figure depicts how these technologies could be organized to support the challenges of the mobile edge.
NFVO is an important element for assured C2 communications to the mobile edge. The NFVO provides the glue from the Data Center gateway to the virtual radio base station – it covers the full distributed environment. It orchestrates routes for local IP breakouts to the Secure Message Fabric service and provisions Virtual Network Functions (VNFs) as needed. It synchronizes the network elements at each level to ensure consistency of performance. It works with ACD Response Controllers to provide security and resiliency across the distributed network.
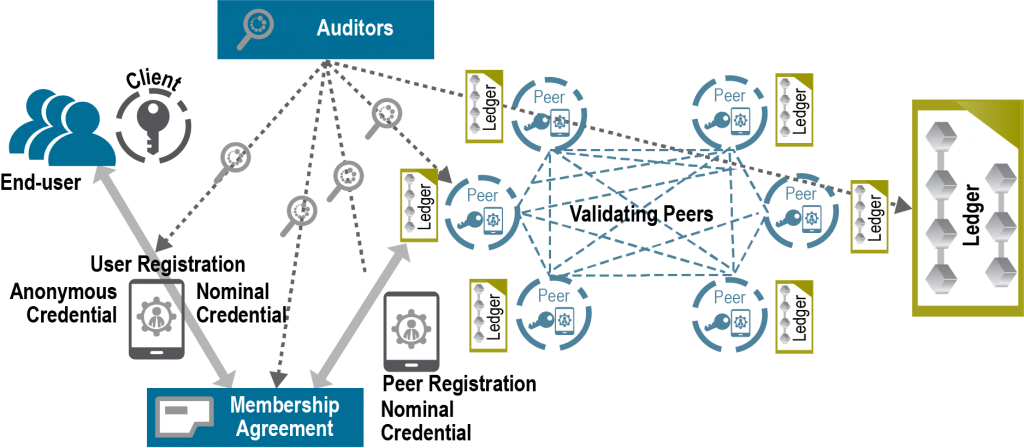
The Secure Message Fabric enables secure message dissemination and storage capability across distributed elements of the ACD environment. It is designed for intrusion tolerance so it can be leveraged where the ACD environment experiences a high degree of adversary activity. ACD C2 messages would be recorded and shared via this fabric. The Secure Message Fabric is based on distributed ledger technology (Block Chain) – see diagram – to ensure immutable records of C2 commands and events are created, disseminated and stored, and to provide a trusted mechanism for sharing threats and cyber events as part of the Information Sharing Services. The Secure Message Fabric may be used to record and share mission-related C2 messages and provides the ability to manage the access permissions / user attributes involved in the sharing community.
The diagram, in particular, depicts an architecture being developed by the Hyperledger Project which is capturing a variety of use cases. It specifically supports a permissioned ledger environment to control access. The files that are created are immutable through cryptographic means, and the mesh network ultimately provides a means to extend a protected network to the edge – a network that has built in capabilities for information sharing.
A distributed ledger service emulates a “trusted” computing service through a distributed protocol, run by nodes connected over the Internet. The service represents or creates an asset, in which all nodes have some stake. The nodes share the common goal of running the service but do not necessarily trust each other for more. As such, the fabric implements an intrusion-tolerant system based on Practical Byzantine Fault Tolerance (PBFT) replication for maintaining consensus among peer nodes. An intrusion-tolerant system maintains its security properties (i.e., confidentiality, integrity and availability) despite some of its components being compromised by an intelligent adversary.
As the fabric implements a permissioned ledger, it contains a security infrastructure for authentication and authorization. It supports enrollment and transaction authorization through public-key certificates, and confidentiality for chaincode realized through in-band encryption. More precisely, for connecting to the network every peer needs to obtain an enrollment certificate from a Certificate Authority (CA) that is part of the membership services. It authorizes a peer to connect to the network and to acquire transaction certificates, which are needed to submit transactions.
A virtual radio access network, in essence, is a base station that consolidates processing on standard server technology to form a resource pool that can support 10~1000 cell towers with software defined radio. Scheduling and processing is accomplished using virtualized network functions (VNFs). The VNFs are controlled by a local SDN controller. Besides the elasticity and agility you get from virtualizing, you also get SWAP gains and lower OPEX. This type of architecture can be delivered by the service provider or met through organic capabilities.
Your Migration to Active Cyber Defense Will Require Culture Change and Skills Enhancement
Significant infrastructure and process changes are necessary to improve cyber defenses so as to keep pace with the ever-increasing volume and level of sophistication of cyber threats. These improvements can realistically only be obtained by achieving a high degree of automation in security operations through machine-to-machine interaction; leveraging emerging technologies such as machine learning and data analytics to augment human cognition; applying standards for exchanging threat and cyber response information; and, using secure open APIs, micro-segmentation, and emerging standards for communicating cyber C2 information. These innovations and changes can greatly decrease the time to incident resolution, provide proactive and predictive defenses to fend off attacks early, provide better cyber protection of assets, and reduce the workload of SOC analysts.
Tools are readily available today to enable these active cyber defenses. Security orchestration vendors offer a high number of pre-integrated capabilities already, with more on the way. Research conducted by NSA, DHS and others have demonstrated significant benefits in reducing detection and mitigation times for a high volume of cyber events through the use of these technologies.
Cultural changes and skill enhancements are also needed to move forward. Machine-to-machine (M2M) interactions are essential to enable speed-to-capability. Machine learning is also important to streamline sense-making and decision-making processes. Reliance on these technologies will require a cultural shift by SOC analysts and managers. The possible negative views regarding this transition can be lessened over time by providing human-assistive machine learning where automated COA recommendations along with supportive evidence and rationale are provided to the SOC operator, with final decision-making made by the operator. The skill base of operators must also be enhanced as new network virtualization technologies take hold and are used to orchestrate cyber defenses.
Don’t think of robots as replacements for humans — think of them as things that will help make us better at tackling many of the problems we face.
EOIN TREACY, “How to profit from the peaceful rise of the robots”, Money Week, April 21, 2016