Johns Hopkins University Applied Physics Lab (JHU APL) hosted a “Community Day” October 5th to highlight some of the research conducted on behalf of the Department of Homeland Security (DHS – Dr. Peter Fonash) and the National Security Agency (NSA – Mike Herring) on “Integrated Adaptive Cyber Defense” or IACD. Wende Peters of JHU APL, the overall research manager of the effort, spent a couple of hours reviewing the project’s progress to date and provided some information on the roadmap for the effort. You can find her slides here. IACD has been underway for a few years now and so far the results look promising but still early.
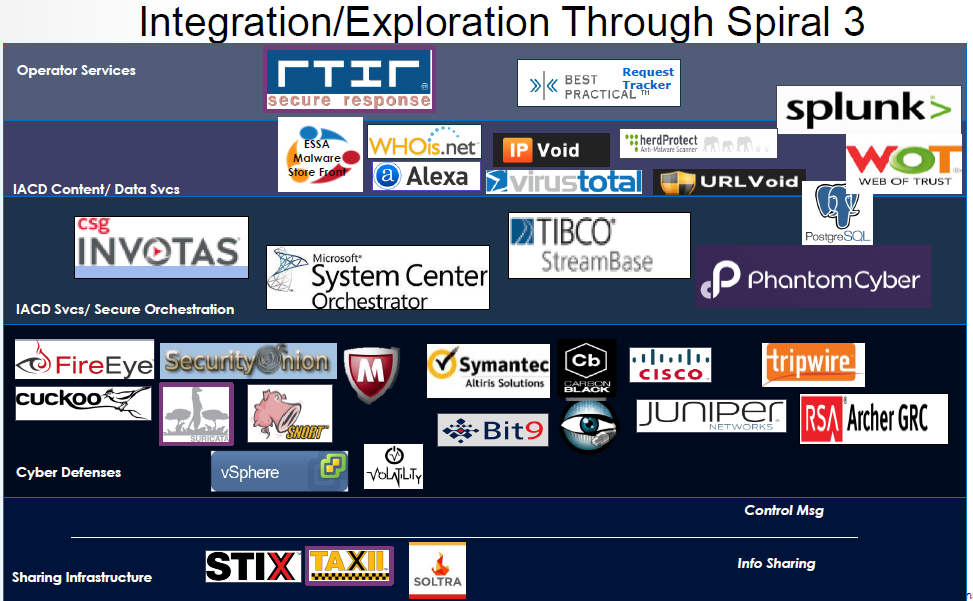
The primary focus of IACD is to research and demonstrate secure integration and automation across a diverse, changeable array of cyber defense capabilities with the ultimate goal of reducing the cyber response time to attacks or breaches from days or months to minutes or seconds. Information sharing also plays a key role in the research as JHU APL looks at commercial technologies and emerging standards such as STIX/TAXII to help enterprises quickly share indicators of compromise (IOCs) and courses of action (COAs) across “communities of trust.” The prompt sharing of IOCs and COAs, it is believed, will help accelerate the sense-decide-act loop for security events and disrupt the kill chain before damage can occur across the enterprises that comprise the respective community of trust. So far the research has been conducted over four integration spirals – see Chart.
Each of the spirals added a new mix of technology to the overall integration fabric while also pushing the envelope on scaling and performance goals. For example, Spiral 0, which focused on accelerating the sense-making-to-decision timeline while supporting a significant operational workload, was able to reduce the timeline from hours / minutes to minutes / seconds while also increasing triage capacity by over 10000x. Other spirals saw similar successes including reducing COA response timelines by 98%, enabling early warning and protection from attacks among community members down to minutes, increasing the speed and efficiency of indicator processing to realistically enable re-direction of operational resources to focus only on high impact/risk areas, and increasing the complexity of COA processing and sharing. The chart below shows the overall framework and vendors involved through Spiral 3.
Several challenges remain to be investigated in future spirals. Spiral 4, which is in the planning phase, entails the addition of a messaging / control plane fabric to to begin to elicit performance and access control requirements while continuing to evolve the COA sharing framework. Future spirals are likely to address SDN/NFV for orchestrating security responses, the use of deception to expose adversary TTPs, and autonomous endpoint protections.
Other issues are also beginning to emerge that could affect this research as well as its transition to full-scale operations. For example, I was speaking to a researcher of a leading malware detection vendor recently who expressed some reservations about the sharing of IOCs. The researcher explained that as attacks become more targeted, resulting in very specific IOCs, the efficacy of sharing IOCs may diminish. Both technology and policy improvements are needed around COA sharing as well. Mileage will likely vary greatly from enterprise to enterprise for reuse of COAs due to differences in technology, policy, and mission impact. Just as many enterprises test patches before applying them, enterprises will need COA rapid simulation capabilities as well to walk through the COA for their specific environment. The “trust” measures in place in a community of trust must also be looked at to ensure that COAs cannot be spoofed and that a high level of confidence can be placed on their effectiveness. Finally, the number of moving parts involved to support any significant use case can seem daunting. Vendors are moving quickly to smooth out the integration rough edges, and many tools are already widely used in the enterprise, however, it is likely that early adopters will need some heavy lifting to get going. Even with these issues looming, the future looks bright for ACD, as the measurable positives appear to far outweigh the negatives, but it is still early in the process.
Where is your enterprise in the use of active cyber defenses? What tools do you currently possess that can be leveraged in active cyber defenses? What pros and cons do you foresee in adopting active cyber defenses? Share your thoughts and experiences and keep checking in for more ACD news, articles, and interviews.